In the complex landscape of the modern internet, certain terms and phrases suddenly attract intense attention. One such phrase that has been gaining traction recently is “thejavasea.me leaks aio-tlp371.” To the casual observer, it may look like a random string of letters. But when you dive deeper, it becomes clear that this phrase is tied to broader conversations about data exposure, cybersecurity risk, digital leak culture, and online privacy concerns. As more internet users encounter these terms, understanding what they mean, where they come from, and how they impact both individuals and organizations becomes essential especially in a time when data leaks and privacy breaches are increasingly common.
The intent of this article is not just to define the term but to provide practical, clear, and fact‑based guidance about its implications, associated risks, and responsible behavior online. We’ll explore the likely meaning of thejavasea.me leaks aio‑tlp371, how such leaks are discussed in cybersecurity circles, the risks they pose to personal data and systems, and importantly, how you can protect yourself from harm. By the end of this guide, you will have a thorough understanding of the context, significance, and safe handling of information connected to this keyword.
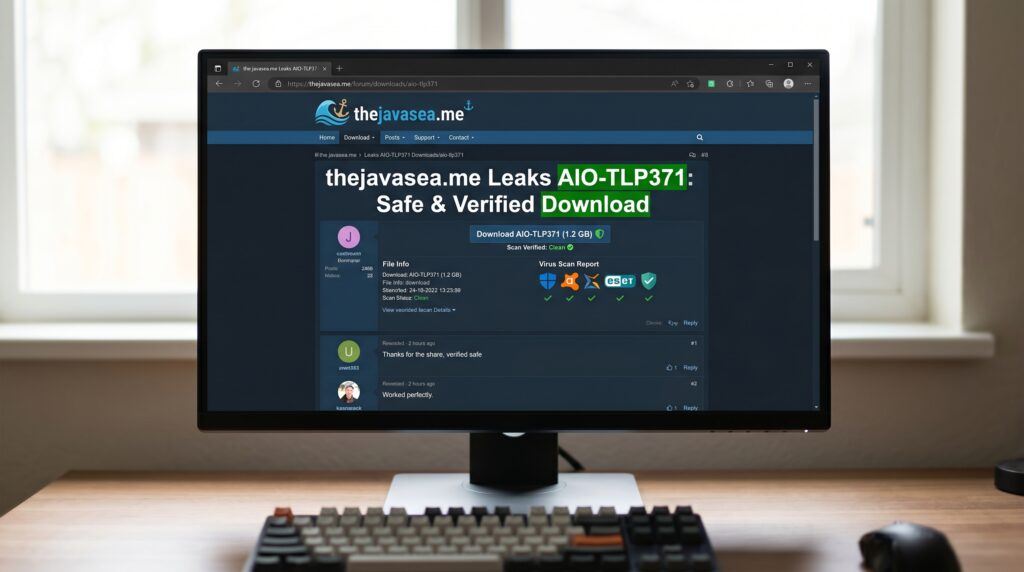
What thejavasea.me Leaks AIO‑TLP371 Refers To
When you search for thejavasea.me leaks aio‑tlp371, what you’re typically encountering is a reference to a reported data exposure incident linked to a site called thejavasea.me. According to multiple cybersecurity news observations, thejavasea.me has become associated with discussions surrounding data leaks specifically large compiled datasets that appear to have been exposed publicly without proper authorization.
In cybersecurity terminology, AIO stands for All‑In‑One, suggesting that a leak includes combined data from multiple sources or breaches. The code TLP371 appears to act as a specific identifier or classification for this particular leak package. In one interpretation reported by privacy communities, AIO‑TLP371 is not simply a small set of leaked data it is a compiled collection of information drawn from multiple breaches. This composite format makes it especially relevant to both cybersecurity professionals tracking leak incidents and to users worried about personal exposure.
The exact contents of AIO‑TLP371 are not directly published by official entities, which means confusion and speculation circulate widely online. Nonetheless, experts discussing this type of leak suggest that the dataset may contain sensitive personal details such as email addresses, usernames, passwords, IP addresses, or other private information aggregated from various breaches. This is consistent with how compiled “AIO” leak packages have been used in other known cybersecurity contexts.
Why This Leak Has Drawn Widespread Attention
The reason keywords like thejavasea.me leaks aio‑tlp371 gain traction is not only because of the potential sensitivity of the data involved but also because of how rapidly such topics spread online. When people hear the word leak, they often assume the worst that personal or private information has been exposed without permission. This fear quickly leads to search surges, social media amplification, and widespread discussion on forums and messaging platforms.
Unlike verified breach disclosures by official organizations (such as government agencies, cybersecurity firms, or regulated corporations), leaks discussed in forums or loosely moderated platforms are often poorly documented and lack transparent details. This uncertainty feeds curiosity, speculation, and sometimes misinformation. As a result, internet users may search for terms like this out of concern for their own privacy, or simply to understand what others are talking about.
Data leak keywords also attract attention because of the all‑in‑one nature of such packages. Combining leaked data from different sources into a single downloadable dataset as suggested by the “AIO” portion means a broader footprint of information could be exposed. When such a leak is referenced by an identifying tag like TLP371, it signals to some communities that the incident is part of an ongoing sequence or series of related exposures.
How Compiled Leak Packages Like AIO‑TLP371 Are Constructed
Compiled leak packages like AIO‑TLP371 are not typically the result of a single security breach. Instead, they represent aggregated collections of data pulled from multiple sources. These sources might include smaller breaches, older leak archives, or breached databases that have been combined into one exportable dataset.
For example, one source explains that AIO leak packages often include email addresses paired with passwords, usernames from various platforms, IP metadata, and other personal identifiers drawn together. Because this combined structure brings different pieces of information into one place, the risk profile increases compared to a single breach with isolated exposure.
This structure poses dangers beyond simple data visibility. When credentials from different breaches appear together, they can facilitate credential stuffing attacks automated attempts to use known email/password combinations across multiple platforms. This is particularly effective when users reuse the same password across services.
Another concerning aspect is that packaged leak data can make it easier for malicious actors to perform targeted phishing, social engineering attacks, and identity theft. With more consolidated information in one place, attackers have a clearer picture of targets, increasing the likelihood of exploitation.
Risks Associated With Accessing and Interacting With Leak Data
Interacting with alleged leak data whether through searches, downloads, or forum discussions comes with multifaceted risks. While many users treat leaks as a passive information issue, the consequences can be far more serious. Here are the primary risk categories experts emphasize:
1. Personal Data Misuse: If your email, password, or other identifiers appear in a leak, malicious actors can attempt to access your accounts.
2. Identity Theft: With enough personal details, attackers can impersonate you for fraudulent transactions or unauthorized access.
3. Credential Stuffing: Automated tools can test your known credentials across multiple sites, taking advantage of password reuse.
4. Spam and Phishing: Leaked emails often lead to more spam, deceptive messages, and crafted phishing attempts.
5. Malware and Scam Downloads: Websites that claim to host leak files including ones referencing thejavasea.me may be designed to distribute malware rather than actual data.
Because of these possibilities, cybersecurity professionals advise not downloading or interacting with leak packages from unverified sources. These files may not only compromise your privacy but could also contain malicious code meant to infect systems or steal credentials.
How to Check Whether Your Data Was Affected
If you’re concerned that your information may have been included in a data leak such as AIO‑TLP371, there are reliable ways to check without exposing yourself to risk. One of the most widely trusted tools is Have I Been Pwned, a publicly accessible database of known breaches.
To use this service:
-
Visit haveibeenpwned.com
-
Enter your email address
-
The site searches across confirmed datasets and reports where your information appears
If your email shows up in association with any known breach including those similar to AIO‑TLP371 it’s a strong indication you should take immediate protective steps. Note that this service does not require you to download anything and does not store your search results.
Practical Steps to Protect Yourself
Once you’ve established that your details may have been part of a leak or simply want to act preemptively, there are concrete steps you can take:
Change passwords immediately: Use strong, unique passwords for every account you hold.
Enable two‑factor authentication (2FA): 2FA adds an extra verification layer, making it harder for attackers to access accounts even with a leaked password.
Use a password manager: Tools like Bitwarden generate and store unique passwords, preventing reuse.
Monitor financial accounts: Keep a close eye on bank statements for unusual activity.
Avoid unsafe downloads: Do not download files from unverified leak websites.
These steps strengthen your defenses against unauthorized intrusion and reduce the potential damage of any exposure.
Cybersecurity Awareness: A Broader Imperative
Keyword spikes like thejavasea.me leaks aio‑tlp371 are reminders of the broader digital security challenges facing individuals and organizations. In today’s data‑driven world, personal information is constantly at risk from corporate breaches to third‑party vulnerabilities and hacker exploits.
Being proactive about cybersecurity is no longer optional. It means adopting protective habits such as regular password updates, cautious browsing behavior, and skepticism toward unverified sources to safeguard personal and professional assets. Education, vigilance, and responsible digital practices help reduce risks and protect individuals from becoming the next victim of identity theft or account compromise.
Read More: thejavasea.me Leaks AIO‑TLP371: Safe & Verified Download
Final Thoughts
The attention around thejavasea.me leaks aio‑tlp371 underscores a key truth about the modern internet: Not all information appearing online is safe, verified, or accurate. Keywords or discussions about data leaks touch on real risks, but they are also surrounded by speculation, noise, and sometimes misinformation.
For users navigating these topics, careful, informed, and cautious approaches matter most. Avoid engaging with unverified download sites, prioritize your personal security, and treat leak discussions as potential red flags rather than invitations to download unknown files. The best way to protect yourself is not just through tools but through awareness, skepticism, and everyday cybersecurity habits.